Switch to a Better
Medical Waste Disposal Solution
with MedPro Disposal
Save Money
We save the average customer up to 30% off their current medical waste disposal and compliance services rate.
Peace of Mind
We take full title to your waste and carry the most comprehensive insurance, offering 100% protection.
On-Time
You’ll enjoy 99% on-time medical waste management service and have access to a dedicated customer advocate.

Trusted
Work with the most trusted provider in the industry, with the most customer testimonials and reviews online.
MedPro Disposal Provides Services to Meet Your Needs
From medical waste management services to document destruction with compliance ensured along the way, MedPro Disposal is here to help.
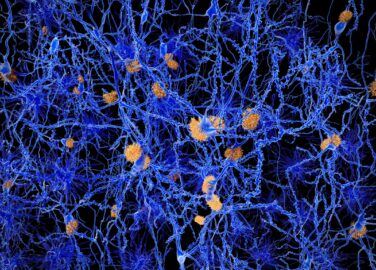
Medical Waste Disposal
Medical waste is any kind of waste that contains infectious material (or material that’s potentially infectious). This definition includes waste generated by healthcare facilities like physician’s offices, hospitals, dental practices, laboratories, medical research facilities, and veterinary clinics.
Compliance Training
Our compliance suite includes training modules and certification services covering everything from OSHA-mandated employee training to your facility’s HIPAA and PCI compliance requirements. Our online solution is available 24/7.

Data and Document Destruction
We’ll destroy documents and data for you in the right way to ensure personal privacy is respected and you’re meeting HIPAA compliance laws. MedPro Disposal offers practices the option to select a secure data destruction service to help ensure continued compliance.

Pharmaceutical Disposal
We provide an environmentally-friendly and cost-effective solution for disposing of your facility’s unused or expired pharmaceutical waste. From over-the-counter (OTC) to Scheduled II-V DEA-regulated medications, we have solutions to ensure compliance.
Industries We Serve

Hospitals
From smaller community hospitals to 100+ bed facilities, we offer solutions to meet your needs.

Physician Practices
Urgent care clinics have increased, we’ve grown our operations to provide an alternative solution.

Emergency Care Clinics
Urgent care clinics have increased, we’ve grown our operations to provide an alternative solution.

Long-term Care Clinics
With flexible service options, we can meet the needs of clinics where disposal needs may vary by season.
Funeral Homes
We offer funeral homes a safe and compliant solution to dispose of infectious materials.

CHOOSE GREEN!
MedPro Disposal is
Committed to the Environment.
We utilize environmentally friendly disposal options across the nation. From fuel-efficient vehicles to disposing of our client’s biohazard waste with the use of steam-powered autoclave machinery, we make every attempt to minimize our impact within local communities.
Try this quick medical waste disposal calculator
How much should you be saving? Find out now!

Make the Switch
Since our founding in 2009, thousands of healthcare providers have trusted MedPro Disposal to manage their medical waste and compliance training needs.

30%
COST SAVINGS
25000+
PRACTICES

48
STATES SERVICED

99%
ON TIME
Informational Content

Informational Content
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Pellentesque malesuada elit eget
Lorem ipsum dolor sit amet,
consectetur adipiscing elit.
Lorem ipsum dolor sit amet, consectetur adipiscing elit. Pellentesque malesuada elit eget consectetur dictum. Nulla tincidunt aliquet velit, sit amet cursus ante commodo et.
Simple and easy
Getting Started
Environmentally friendly and safe
The Disposal Process
Peace of mind
Providing You With Protection
Tailored to fit your needs
Understanding You
One charge
Simple invoices
Our Blog
Keep up to date with industry and disposal information on MedPro’s blog.
Exploring the Link Between Fiber Intake and Diabetes Risk Reduction
Exploring the Link Between Fiber Intake and Diabetes Risk Reduction Recent scientific investigations have illuminated a potential correlation between dietary…
A Guide to Safety and Treatment of Preventing Dog Bites
A Guide to Safety and Treatment of Preventing Dog Bites Dog bites are expected, with over 4.5 million incidents reported…
Understanding the Limitations of Alzheimer’s Plaque-Attack Drugs
Understanding the Limitations of Alzheimer’s Plaque-Attack Drugs In recent news, the withdrawal of aducanumab—a drug aimed at treating early-stage Alzheimer’s…